Contents
- 1 Ignore spam and back up your system –
- 2 Cell phones
- 3 Install a security app –
- 4 Turn off autocomplete and Bluetooth –
- 5 Avoid using unsecured public wifi –
- 6 Use better and strong passwords –
- 7 Online accounts
- 8 Get rid of suspicious mails –
- 9 Use secure devices –
- 10 Beware of the ‘save my info for next time’ feature –
- 11 Let your account alert you –
- 12 What to do if the device or account is already hacked?
- 13 Conclusion
Ignore spam and back up your system –
The need to beware of unknown messages, especially ones with links, cannot be emphasized enough. However, given the changing ways to do the same with messages that mimic the identity of someone you know, it further intensifies the need to take extra care and precautions. Backing your system is a good way to ensure that not everything is lost, even if you fall prey to hacking. An external hard drive backup can make it so you can make up for the data loss and breach without suffering a crisis. Other methods include using two-factor authentication, encryption, virtualization, etc.
Cell phones
Install a security app –

Like firewalls, anti-virus, etc., are for computers, one could also use a security app on a mobile device downloaded from app stores for better security. However, make sure anything you choose to download comes from a trusted source.
Turn off autocomplete and Bluetooth –
Turning off Bluetooth when not in use makes it one less way for hackers to get in. Similarly, autocomplete, a feature that guesses the rest of the sentence as you type, is yet another feature that gives hackers access to your data. So, make sure you turn the autocomplete feature off.
Avoid using unsecured public wifi –

Public wifi connects to your network that many others are using, not to mention how easy and ideal of a target that is for the hackers.
Use better and strong passwords –
Do not give the hackers a chance to guess your passwords. Instead, choose a random combination of numbers that do not relate to your personal information in any way.
Online accounts
Get rid of suspicious mails –

Delete anything that looks the least bit suspicious or spam-like without interacting with it. As for other emails you were not expecting with the identities of someone you know, try contacting the person for the same to confirm it’s theirs before opening them.
Use secure devices –
Do not log into your accounts, social media, or otherwise on any random devices, especially public PC’s which have good chances of being infected with a virus or spyware. Only use your personal device with security measures in place to access anything that another person could use for illicit activity.
Beware of the ‘save my info for next time’ feature –
While the feature to save details given by multiple sites online is helpful, it also makes you vulnerable to any hack on that site. The hacker can easily access the banking credentials and passwords on a site if you choose to save the details on site.
However, if you choose to save it, ensure that the site’s URL begins with HTTPS, where ‘s’ stands for security.
Let your account alert you –
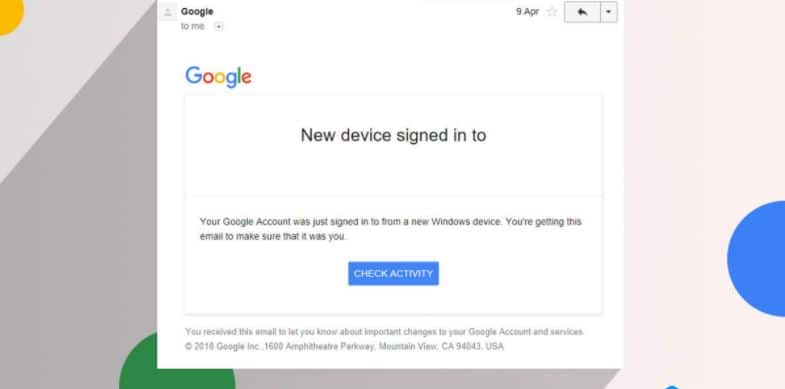
Switching one account alerts is a good way to keep a tab on any unusual activity on the account. The alerts notify a person of any new device which attempts to log in to your account. Upon receiving any such alert, make sure you quickly change your password and deny access to the account.
What to do if the device or account is already hacked?
Despite the efforts, if you find that your account or device has been hacked, make sure to take the following actions without delaying or panicking –
-
- Report hacking and get your devices inspected for the same.
- Change passwords for further protection of personal information.
- Keep an eye on the financial activity on each of your accounts.
- Let your friends and family know about the hack to prevent a chain of damage in terms of personal relationships and future hacks to your contacts.
Conclusion
In recent years, the art of hacking has been increasingly exploited for illicit purposes, and therefore, the need to secure one’s devices and accounts has grown further intense. Making oneself aware of the possibility of hacking, the reasons, and ways out is the first step to a secure connection. One can also take the help of an expert to ensure that their business and website are hack-proof to secure their critical data elements.